In today’s digital world, cybersecurity is no longer optional—it’s essential. Whether you’re browsing social media, running a business, or managing financial transactions, your data is constantly at risk. With cyber threats evolving rapidly, understanding cybersecurity has become crucial for everyone.
This comprehensive guide will walk you through everything you need to know about cybersecurity—from basic concepts to advanced protection strategies—so you can stay safe online.

What is Cyber Security?
Cybersecurity refers to the practice of protecting systems, networks, and data from digital attacks. These attacks are often aimed at accessing, changing, or destroying sensitive information, extorting money, or disrupting normal operations.
In simple terms, cyber security is your digital defense system.
Why is Cyber Security Important?
Cyber threats are increasing at an alarming rate. From individuals to large corporations, no one is immune.
Key Reasons Why Cyber Security Matters:
- Protects personal data (passwords, bank info)
- Prevents identity theft
- Safeguards business operations
- Ensures privacy and confidentiality
- Avoids financial loss
Without proper cyber security, even a small mistake can lead to serious consequences.

Types of Cyber Security
Cyber security is a broad field. Here are the main types you should know:
1. Network Security
Protects internal networks from unauthorized access and attacks. It includes firewalls, antivirus software, and intrusion detection systems.
2. Application Security
Ensures that software and applications are secure from threats. Developers use secure coding practices and regular updates.
3. Information Security
Focuses on protecting data integrity and privacy, both in storage and during transmission.
4. Cloud Security
Protects data stored in cloud platforms like Google Drive or AWS from breaches and leaks.
Common Cyber Threats
Understanding threats is the first step to prevention.
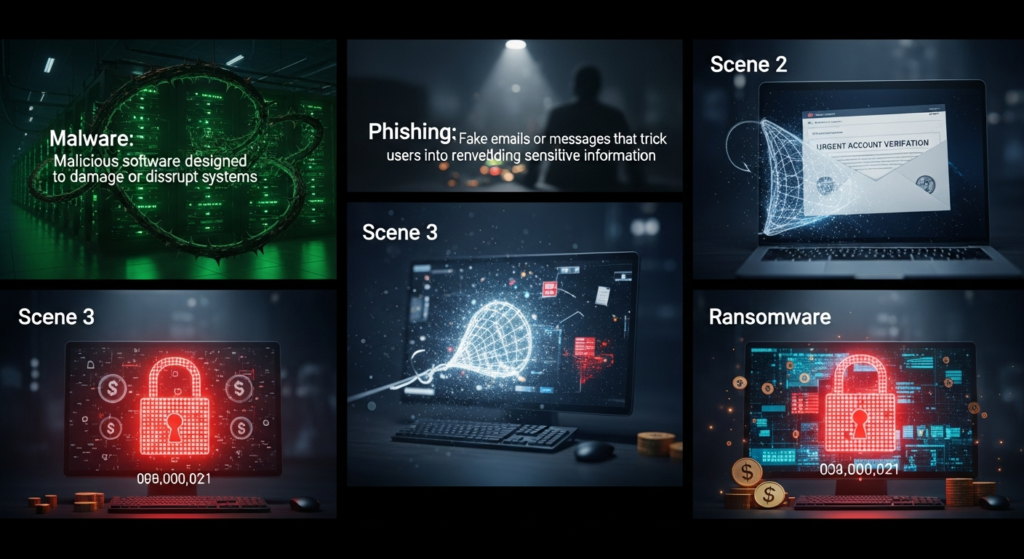
1. Malware
Malicious software designed to damage or disrupt systems.
2. Phishing
Fake emails or messages that trick users into revealing sensitive information.
3. Ransomware
Locks your data and demands payment to restore access.
4. Man-in-the-Middle Attacks
Attackers intercept communication between two parties.
5. DDoS Attacks
Overloads systems to make them unavailable.
Best Practices for Cyber Security
Protecting yourself doesn’t require advanced skills—just smart habits.
Use Strong Passwords
Create complex passwords using letters, numbers, and symbols. Avoid using the same password everywhere.
Enable Two-Factor Authentication (2FA)
Adds an extra layer of security beyond passwords.
Keep Software Updated
Updates often include security patches.
Avoid Suspicious Links
Never click unknown links in emails or messages.
Use Antivirus Software
Install trusted antivirus tools to detect threats early.
Cyber Security for Businesses
Businesses are prime targets for cyber attacks. A single breach can cost millions.
Essential Steps for Businesses:
- Conduct regular security audits
- Train employees on cyber awareness
- Backup data regularly
- Use secure networks and VPNs
- Implement access control systems
Latest Trends in Cyber Security (2026)
Cyber security is constantly evolving. Here are the latest trends:
AI-Powered Security
Artificial Intelligence is being used to detect and respond to threats faster.
Zero Trust Architecture
No one is trusted by default—even inside the network.
Cloud Security Focus
With more businesses moving online, cloud protection is critical.
IoT Security
Devices like smart homes are becoming new targets.
Cyber Security Tools You Should Know
Here are some popular tools:
- Antivirus Software (e.g., Norton, McAfee)
- Firewall Protection
- Password Managers (e.g., LastPass)
- VPN Services
Real-Life Example of Cyber Attack
In recent years, major companies have faced data breaches affecting millions of users. These incidents highlight the importance of strong cyber security measures.
Tips for Staying Safe Online
- Don’t share personal info publicly
- Use secure Wi-Fi networks
- Log out from shared devices
- Monitor your accounts regularly
Recommended Resources
For further learning, check these trusted sources:
- https://www.cisa.gov (Cybersecurity & Infrastructure Security Agency)
- https://www.kaspersky.com/resource-center
- https://www.cybersecurityguide.org
Conclusion
Cyber security is not just a technical topic—it’s a necessity for everyday life. As cyber threats continue to grow, taking proactive steps can save you from serious risks.
By understanding the basics, staying informed, and following best practices, you can protect yourself and your data effectively.





